Q1 2026 Cyber Threat Report
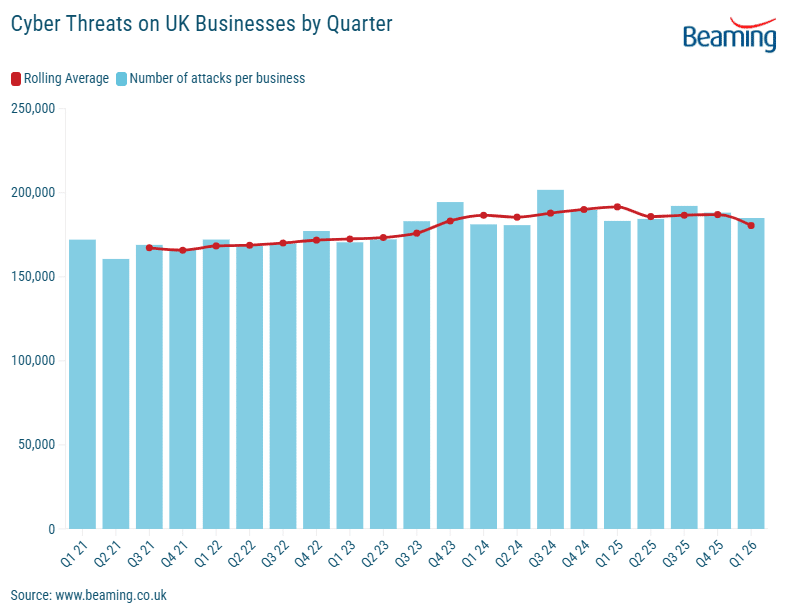
The first three months of 2026 have seen UK businesses continue to operate under a sustained level of cyber threat. Analysis of the latest data shows that while the volume of attacks has plateaued compared to the record highs seen in late 2025, the intensity of activity remains significantly elevated compared to historical norms.
Attack volumes remain high
Between January and March 2026, UK companies were targeted by an average of 1,988 cyberattacks each day. While this represents a slight 2% decrease from the daily attacks recorded in the final quarter of 2025, the figure is almost identical to the activity levels seen during the same period last year.
The consistency of these figures suggests that high-volume automated probing has become a permanent fixture of the UK’s digital landscape.
Shift in attacking infrastructure
While the number of attacks per business remained steady, there was a noticeable shift in the underlying infrastructure used by attackers. The number of unique IP addresses identified as sources of attack fell by 14.6% in Q1 2026 compared to the previous quarter.
This trend indicates that although fewer unique devices are being used to launch attacks, those that remain active are being used more intensively.
Applications under fire
Remote control applications and file sharing services continue to be the primary focus for automated attack scripts. These services are often targeted because they can provide a direct gateway into a business’s internal network if not properly secured.
A significant trend observed is the growing intensity of attacks directed at web applications. While automated scripts continue to probe for any available weakness, there has been a marked and steady increase in the volume of attempts to breach web-based services.
This shift is particularly concerning as businesses increasingly move their core operations and customer interactions to the cloud. Attackers are clearly refining their methods to target the public-facing side of UK businesses, looking for vulnerabilities in websites and online portals that could serve as a gateway to sensitive business data.

Geopolitics and the cyber landscape
The geographical origin of cyberattacks continues to reflect the influence of global events on the digital environment. In Q1 2026, China and the USA remained the most common locations for attacking IP addresses.
However, the data often shows fluctuations in activity from specific regions that coincide with shifts in international relations and local infrastructure changes. Business leaders should recognise that cyber threats do not exist in a vacuum; changes in the physical world frequently dictate the focus and origin of digital hostility.

Advice for UK businesses
As the baseline for cyber activity remains high, business leaders must ensure cyber defences remain a constant consideration.
- Review remote access: With remote control tools remaining a top target, ensure all such applications are protected by multi-factor authentication (MFA) and are only accessible via a secure VPN.
- Monitor global trends: Understand that shifts in international politics can lead to changes in the type and origin of threats. Ensure your IT team or managed service provider are subscribed to threat intelligence feeds that provide warnings.
- Patching and updates: Many automated attacks rely on exploiting known vulnerabilities in common software. Maintaining a patching schedule remains one of the most effective ways to neutralise high-volume “noise” attacks. The Cyber Essentials update in April 2026 requires patching to be carried out within 14-days of release.
- Employee awareness: Technology is only one part of the solution. Regular briefings for staff on the latest phishing techniques and social engineering tactics help to close the “human gap” in a company’s defences.