Cyber report 2019: Volume of attacks doubles
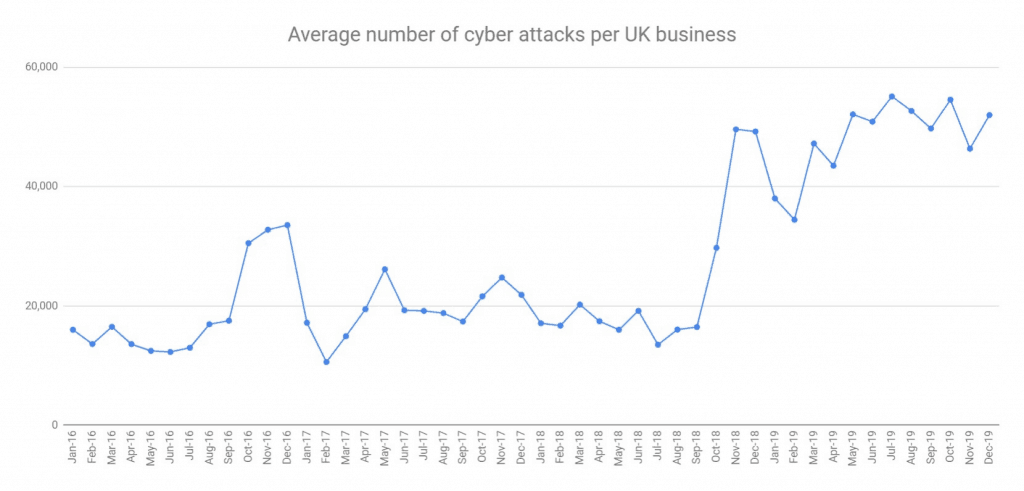
The volume of online cyber attacks on UK businesses more than doubled in 2019, with organisations subjected to 576,575 attacks each, on average, according to our analysis.
The number of internet-borne attacks in 2019 was 152 percent higher than the 281,094 recorded in 2018 and was the largest volume of cybercrime attempts recorded in a single year since Beaming started analysing attacks in 2016. On average, cybercriminals from around the world subjected UK businesses to 66 different attacks every hour during 2019.
Where do the attacks come from?
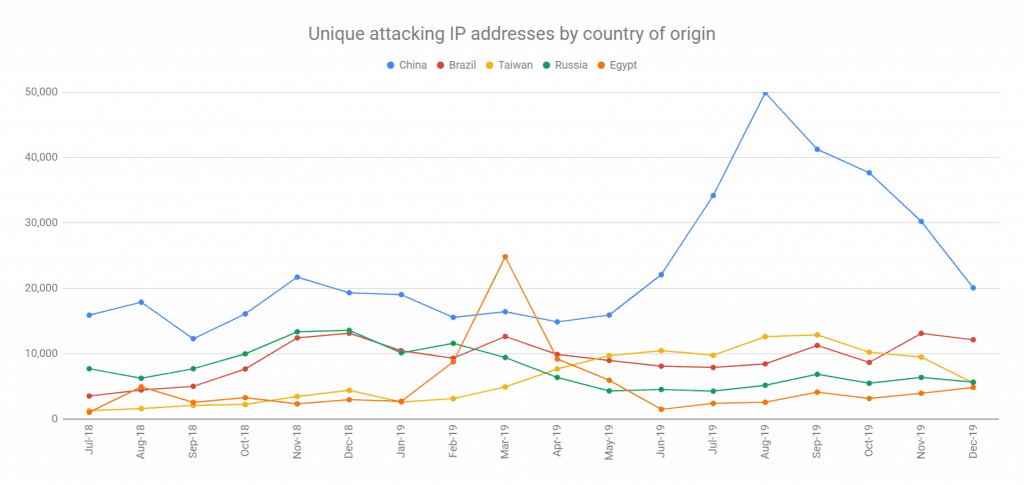
Beaming’s analysts identified 1.8 million unique IP addresses used by cybercriminals to launch attacks on UK businesses during 2019 and traced a fifth (18 percent) of them to locations in China. A significant amount of attack activity also originated from IP addresses located in Brazil (seven percent), Taiwan (six percent), and Russia (five percent).
What applications are targeted?
Network device administration tools and IoT applications such as building control systems and networked security cameras were the most common targets for cybercriminals in 2019, attracting 92,448 online attacks between them. 35,807 attacks sought to compromise file sharing applications.
How can businesses protect themselves from cyber threats?
Sonia Blizzard, managing director of Beaming, comments: “2019 was the worst year on record for the sheer volume and variety of cyber attacks experienced by UK businesses. Our analysis indicates that each UK company with an internet connection was attacked online more than once a minute last year. Most of these were completely indiscriminate.”
“Most business leaders, particularly at the smaller end of the spectrum, still don’t recognise the threat or incorrectly assume that their broadband router and antivirus systems will be sufficient to keep them safe. With the number of companies falling victim to cybercrime increasing each year, it is clear that most need to do more to protect themselves. We advise businesses to put in place multiple layers of protection, use methods such as two-factor authentication, and to secure their data while it travels over the internet.”
Subscribe to the Beaming Cyber Threat Report
Subscribers receive our quarterly cyber threat analysis first, and with exclusive stats and visuals.