Q2 2023 Cyber Threat Report
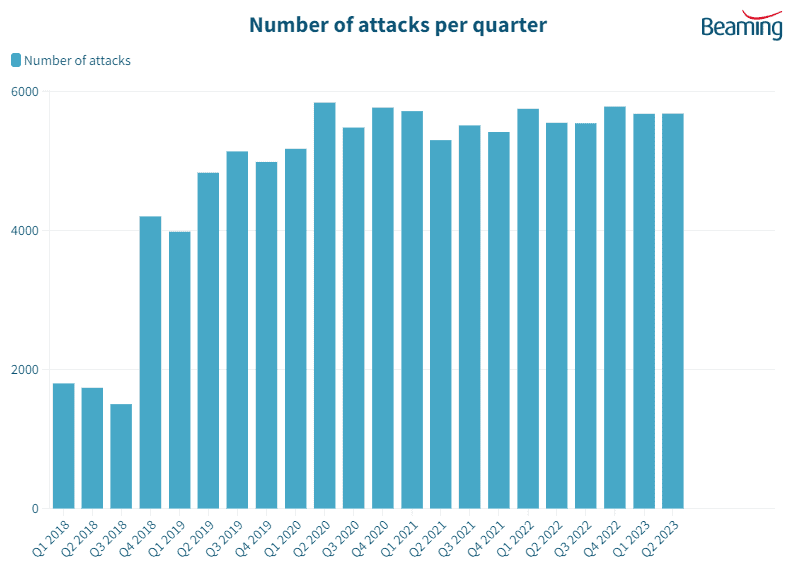
While the number of cyber attacks on UK businesses remained stable in the second quarter of the year, with companies experiencing 172,243 attempts each to breach their systems, hackers increased their efforts targeting file sharing and database applications.
Cyberattacks targeting file-sharing applications increased by 10 per cent between April and June, while the number seeking to exploit vulnerabilities in company databases was up by eight per cent. Companies also experienced a four per cent increase in attacks on VoIP telephone systems.
Devices connected to the Internet of Things continued to be targeted most frequently, attracting more than one in every ten attacks, but the number deliberately targeting these systems fell by three per cent in the second quarter.
Beaming identified 294,404 IP addresses used to launch cyber attacks on UK businesses between April and June. It traced a quarter (25 per cent) of these addresses to locations in China, while India and the USA also appeared to be the source of a significant proportion of attacks.
What can businesses do to protect against cyberattacks?
There are several steps that Beaming recommends businesses take to protect against cyberattacks:
- Use strong passwords and enable multi-factor authentication on all accounts and devices.
- Keep all software and devices up to date with the latest security patches and updates.
- Use a business-grade firewall to protect your network and restrict access to authorised users.
- Use antivirus and anti-malware software to detect and remove any malicious software.
- Educate employees about cybersecurity and the importance of following safe practices when using the internet and company devices.
- Back up important data regularly to protect against data loss from an attack.
- Use a Virtual Private Network when connecting to the internet over public Wi-Fi.
- Consider purchasing cybersecurity insurance to help cover the costs of responding to and recovering from a cyberattack.
- Work with your ISP or a trusted IT provider to help implement these and other security measures.
Beaming are experts in protecting businesses
Our customers trust us to keep their data safe and their systems secure and as a result, we’ve amassed a great selection of our own cybersecurity resources, which we’re happy to share.