Sophos UTM: Gaining SSH access to the slave node from a master node
Posted on 14 May 2019 by Beaming SupportThe ‘issue’ with HA configuration
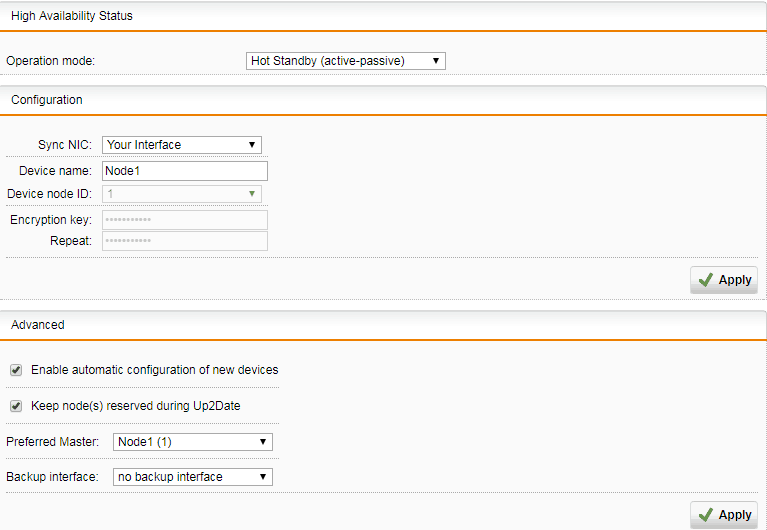
When you set up High Availability (HA) on a Sophos UTM, you simply select the interface your UTMs are connected with as your ‘Sync NIC’, name your device (e.g. Node1), press apply then change the operation mode to Hot Standby (active-passive), like the below.
This is quick and easy to set up, but it’s also easy to forget future diagnostic information e.g. what if I need to get shell access to the SLAVE node? What is the IP address? How on earth are they communicating?
Behind the scenes both actually do get an IP address, more specifically an RFC 2544 address, which is an address space for special IPV4 benchmark testing, reserved by IANA ranging from 198.18.0.0 to 198.19.255.255.
In order to truly understand what we are doing we need to first SSH to our MASTER node.
First gain access to the master node
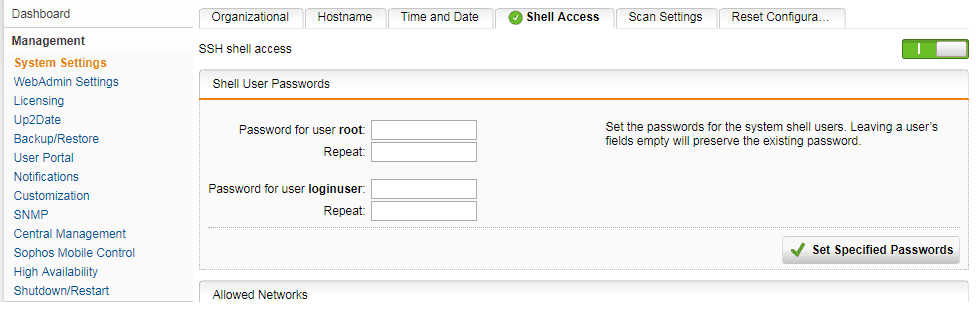
Assuming you have shell access enabled on the MASTER, settings found below, this settings and credentials will replicate to the SLAVE node.
Continue to use your favourite utility for shell access, I’m going to use PuTTy in this example.
NOTE: If this is your first time SSHing into a UTM you need to keep in mind that you first need to log into the ‘loginuser’ before you can elevate your privileges to root (via the SU command).
Now SSH into the MASTER node, you don’t need to gain access to the root account, but if you want to then run the su command when you’re logged in as loginuser.
Now you’re logged into the shell of the MASTER node, we can finally get into the SLAVE node.
Gaining access to the slave node from the master node
There are two powerful commands at our arsenal that help us fully understand what is going on here.
ha_daemon –c status
This will show us the basic status of the HA setup, including the IP address of the MASTER and the IP address of the SLAVE which is assigned across the backup link.
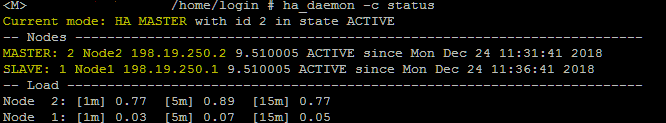
Here we can see that the current mode is HA MASTER, because we are currently logged into the MASTER node.
ha_utils ssh
This is the most useful of commands as this will automatically find the SLAVE’s IP address and will attempt to login as the loginuser via SSH, which will prompt you for credentials.
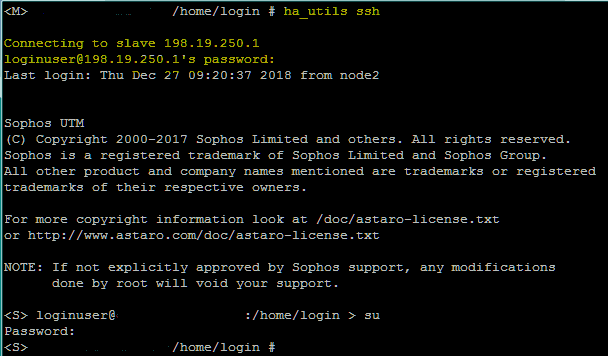
Once you’re logged in, that’s it! You can now check it over.
It’s not often you’re going to need to gain sole access to the slave, being that all changes on the MASTER are replicated to the SLAVE, but on the off chance that you need to you know can have peace of mind that there is a way.
Stay in the loop
Our how-to guides, cyber security advice and productivity tips help businesses stay on track.